Protect your Organizations against Online Attacks
To get protection against online attacks and vulnerabilities online merchants must have SSL (secure socket layer) security, which is in interest of business and customers. Different types of attackers (serious hackers, computer beginners, or dissatisfied current or former employee) could induce a possible threat into organization’s information security. Many attackers take advantage of poor policy and procedure related to information security. Today with the help of internet, anyone can find the information regarding how to manipulate the system by exploiting security weakness on your online business. Attackers may also break security by applying automated tools to look into network systems, and exploits any known security weaknesses to get illegal access to the network.
Attacks and Threat Trend: Symantec has published “Threat Trend report 2013” in which some shocking facts have come out which is worth thinking for online industries. The facts are as below:
- The average number of malicious website-blocked ratio is increased by 30% in 2012. There were 247,350 websites were in the list of blocked website in 2012 compared to 190370 websites in second half of 2011.
- The number of malicious blocks ratio was 37% higher than its annual average.
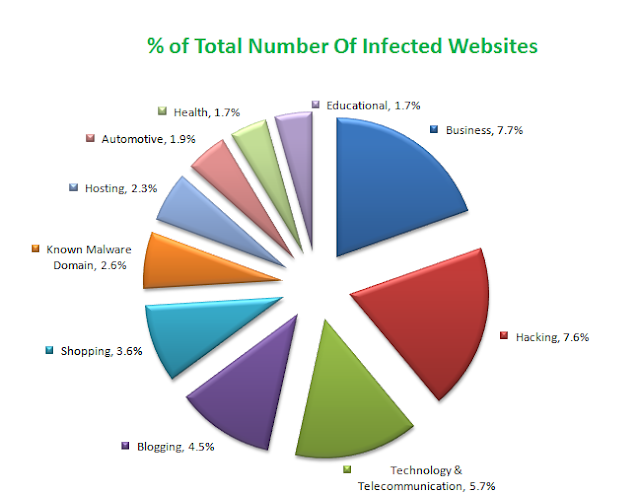
- The most exploited website categories and (percentage) of infected website are as below.
- There are 7.7% websites were malicious was assorted in blogging category.
- 43% compromised religion websites were infected with fraud antivirus attacks.
- 28% compromised business sites were infected with fake antivirus attack.
What is Online Attack: Attack is a term where attacker plays role of a genuine verifier and changes the authentication channel to access the network authentication. There are different types of network attacks, which can bring disasters in network system.
We would like to share the latest security attacks and steps to protect your online business from such attacks.
Steps against Backdoor: There are some tips to save your system against backdoor attacks.
We would like to share the latest security attacks and steps to protect your online business from such attacks.
Backdoor Attack:
Back door also called trap door. It is a part of program code, which is written into application without the awareness of the users and the administrator. It allows fast access to programmers to make easy debugging or monitoring the program. Backdoors typically allow programmers to make use of the software or hardware with the most important rights such as root or administrator. When programmer neglects to remove backdoor after debugging then, a backdoor becomes a serious trouble. Backdoors work mutely in the background and are tough to find out.Steps against Backdoor: There are some tips to save your system against backdoor attacks.
- You can run antivirus to close the backdoor attacks.
- Turn your firewall protection to get alert of any backdoor attack.
- Regular checks the entire program integrity.
- Make rigorous control process and system development.
Brute Force:
Brute Force attack is used against encrypted data then using software to crack the code and gain right to use of USER ID and password. With user ID attacker gains access of privileges and can generate a backdoor for future approach. Brute-force attack includes tries multiple key combination to discover the right password that will unlock the encryption. The higher the encryption is the longer it will take time.
Steps against Backdoor: There are some tips to save your system against backdoor attacks.
- Use strong encryption technology and effectual key management technology to protect User ID, password.
- Periodically change your password
- Run penetration testing to discover vulnerability.
- Give enough education to customers and employees on security precautions.
Denial of Service(DOS):
Denial of Service is a disrupting attack which do not target network access but disturb the network traffic flow by injecting more information on the server than it can control. This kind of attack can be generated at single or multiple sources. Dos attack makes web resources unavailable for common users by flooding the URL with numerous requests.
Steps against DOS: Some tips which can help you to prevent DOS attack and save your system.
- Tell Internet service provider to arrange traffic from authorized sources only.
- Arrange sufficient backup and recovery arrangements.
- Perform penetration testing for assessing the network ability.
In recent time, DDOS attack brings down the internet speed with enormous unnecessary request flaws or dummy traffic. DDOS attack was targeted at Spamhaus, a spam filter company that maintains filters email spammers. The DNS requests used in this attack was 300Gbps.
It is a network security attack that allows attacker to take control of an established connection during its running process. Hijacking attacks generally happen on a remote computer like personal computer. The attacker intercepts the message in a public key exchange and replaces his own public key for the requested message. Therefore, two original parties will appear for communication with each other like server to the client and the client to the server. Thus, attacker seems to be legitimate connection can interpret the message during the transmission.
Steps against Hijacking: Below are steps that can be put into practice for the system to save from hijacking.
Hijacking Attack:
It is a network security attack that allows attacker to take control of an established connection during its running process. Hijacking attacks generally happen on a remote computer like personal computer. The attacker intercepts the message in a public key exchange and replaces his own public key for the requested message. Therefore, two original parties will appear for communication with each other like server to the client and the client to the server. Thus, attacker seems to be legitimate connection can interpret the message during the transmission.
Steps against Hijacking: Below are steps that can be put into practice for the system to save from hijacking.
- Apply strong authentication methods like implementation of SSL security for sending sensitive data.
- Apply firewall setting wherever it fits.
- Monitor network traffic and use scanning tools.
- Implement enough network security.
- Get more.
Sniffers Attack:
Sniffer attack catches network packets it is also called network protocol analyzers that is also applied by hackers for hacking network. Hackers can capture network traffic if it is not encrypted. Once the packet is taken over then attacker can read the message of that particular packet. The message contains passwords, account information, or other confidential information, etc.
Steps against Sniffers: Below are steps that can be placed into practice for the system to save from sniffer attack.
- Apply strong SSL security for sensitive sessions.
- Regularly monitor network traffic and use scanning tools.
- Apply enough network security.
- Provide guidance to customers and employees about security precautions.
Spoofing Attack:
Spoofing attack means to do trick or betray network system. Spoofing allow attackers to hide their identity or communicate with a fake identity which pretend to be a legal identity. Therefore, network recognizes the unauthorized network as an authorized network. Attacker can easily gain access the sensitive data. Spoofing can be done through email spoofing, IP spoofing, fake identity.
Steps against Spoofing: Spoofing is a simple way to make others victim by making a fake username. To prevent from it user can take following steps.
- Apply firewall setting wherever it fits.
- Apply strong SSL security for sensitive sessions.
- Regularly monitor network traffic and use scanning tools.
Man in the Middle Attack:
Man in the middle (MITM) attack also refers to bucket brigade attack in this case attacker sniffs the information transferring between the sender and the receiver like the server and the browser or between two servers. Such information is not encrypted. Attacker collects the information and intercepts it then sends it to the receiver.Steps against MITM: Following are some useful steps to avoid MITM attack.
- Download the latest version of high security web browsers.
- Use Extended Validation (EV) certificate for the highest protection against MITM attack.
- Use two-factor authentication for sensitive accounts.
- Never respond unknown or spam emails.
Phishing Attack:
In Phishing attack, attacker personates to be a legal person or business through fraud emails or websites and illegally acquire sensitive information like username, passwords, credit card information, and bank account details. There should be SSL security (EV certificate) that can provide protection against phishing. Besides, user training and technical measures also need to be implemented.From the above discussion about different online attacks, we can definitely understand that how much essential the SSL is not only from preventing online threats but also helps gain fame and trust from the visitors. It is therefore required to have a strong security called SSL protocol for your online business.
SSL - Secure bridge of Online information:
Now we can imagine that how online attacks have influenced online industries. In this situation, SSL (secure socket layer) can secure your entire website with robust security. SSL is an encrypted technology, enabling the server and the browser to transfer the information in a secure environment. SSL encrypts the information so the hacker could not identify it and user information will remain secure over the web. SSL uses public key and private key to encrypt and decrypt the information.
How SSL Works?: What comes out when a Web browser connects to an SSL secured Website?
How SSL Works?: What comes out when a Web browser connects to an SSL secured Website?
- The first step is that the browser attempts to connect to the website.
- The browser demands the Web server to confirm whether the web site is equipped with SSL security or not.
- The server of the site transmits a copy of the SSL certificate for the visitor's web browser confirmation.
- The next step is confirmation of the SSL security certificate.
- The browser assures that the certificate sent by the SSL web server is trustworthy.
- If the certificate is legitimate, the browser transmits a message to the web server.
- However, if it fails, the browser makes a warning and stimulates the user to authorize or deny the legitimacy of the web server certificate.
At the end, we can summaries that online attacks are expanding their horizon and it is sensible to have a strong network security to prevent online attacks. In this case, SSL stands alone in security criteria that have utmost protection for described online attacks. It allows a secure bridge in which the sender and the receiver can transmit data in a secure environment.
 Labels:
Attack,
Attacks,
Backdoor,
DDOS,
Denial of Service,
DOS,
EV Certificate,
Hijacking,
Man in the Middle,
MITM,
Online Attacks,
phishing,
Sniffers,
Spoofing,
SSL Certificates
Labels:
Attack,
Attacks,
Backdoor,
DDOS,
Denial of Service,
DOS,
EV Certificate,
Hijacking,
Man in the Middle,
MITM,
Online Attacks,
phishing,
Sniffers,
Spoofing,
SSL Certificates





 Previous Article
Previous Article
