Correlation between Dedicated IP and SSL
What is Dedicated IP exactly stand for? This is indeed a basic question that needs to be understood by any techno savvy person. However, before going to reveal about dedicated IP let us understand IP address. IP address serves two main functions including network interface identification and location addressing. Generally, there is 32-bit IP address is in use, which is known as IPv4 but due to growth of internet, IP designers now using 128-bit IP address, which is called IPv6.
There is a lot of debate on whether to choose dedicated IP or not, we have to look at dedicated IP, and other aspects.
Dedicated IP can also provide website speed though multiple source of traffic is handled by a single IP. Every server examines a packet, and request and then deliver the traffic to particular domain. In this case, number of destination is not significant, the process of website loading time can be slightly influenced which is not a serious concern.
What is Dedicated IP?
It is easy to remember and assigned to each device that is participating in computer network used for communication. A dedicated IP is only devoted to a single server and not shared with other server. Many shared hosting providers charge normal fee to provide dedicated IP.Speed and Dedicated IP:
Dedicated IP can also provide website speed though multiple source of traffic is handled by a single IP. Every server examines a packet, and request and then deliver the traffic to particular domain. In this case, number of destination is not significant, the process of website loading time can be slightly influenced which is not a serious concern.
Why SSL needs Dedicated IP?
When you have ecommerce website where online shoppers carry online transactions with their debit-credit card, or with online banking, you need an SSL on your website to protect ongoing transactions between the user and the company server. SSL certificate authenticates the server with IP address and verify the IP address assigned to the particular server. When a client connects to the server for a different domain name, the server gets confused about which certificate to show to the client. This process is defined in below example.Example of SSL and Static IP:
For instance, there are two domains called www.abc.com and www.xyz.com and both domains are hosted on a single IP address (for example 000.000.0.0). Now a person has opted SSL for a domain called www.abc.com on his website with that IP address. However, the person wants to access https://www.xyz.com the browser will check for SSL and if it is fail to make secure connection for particular website, then browser will show a name mismatch error.Advantages of Dedicated IP:
- You have less downtime compare to Shared IP.
- If you are ecommerce merchant then you should have your own SSL with a dedicated IP.
- Many web-hosting providers need a unique IP to access anonymous FTP function.
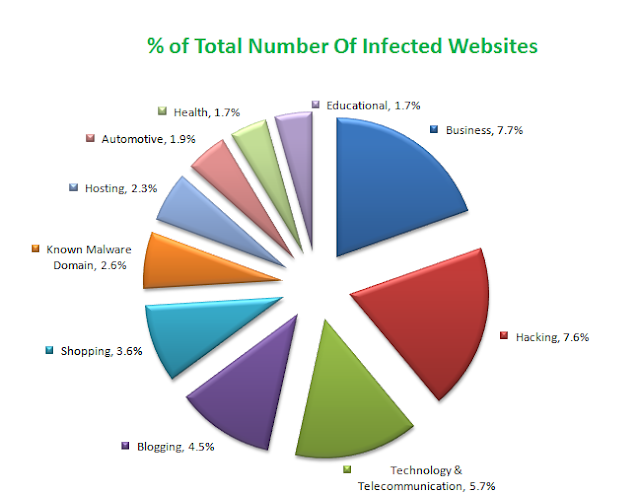
- Shared IP address may have security threat due to shared among multiple website while dedicated IP has less chance of security threats.
- With static IP, you will have easy remote access of your PC from wherever you operate it.
- There are chances of blacklisted website on shared IP address (If there is blacklisted website) on contrary, dedicated IP has less chance of blacklisted.
Alternate Solutions to Dedicated IP:
- SNI (Server Name Indication): SNI is an extension to SSL that allows the client to include hostname in the first SSL handshake so, the server identifies the correct virtual host name for which the request is made, and the server can easily set up the connection.
- Wildcard Certificate: Using Wildcard certificate user can secure unlimited sub domains under a single IP address. You can include sub domains like www.example.com, webmail.example.com etc.
- SAN Certificate: Subject Alternative Name (SAN) can secure up to 25 domain names, sub domains with a single certificate.












 Previous Article
Previous Article
